Hidden Identity Tracing Security Report Log 3512741727 3886957240 3510451818 3201838272 3272772495 3792056290
The Hidden Identity Tracing Security Report Log presents a critical examination of the risks associated with digital identity verification. It highlights vulnerabilities inherent in current technologies and the implications of data breaches. By analyzing these incidents, the report aims to inform stakeholders about the urgent need for enhanced privacy measures. As cyber threats evolve, understanding the balance between anonymity and security becomes increasingly essential. The implications of these findings warrant a deeper exploration of protective strategies.
Understanding Hidden Identity Tracing
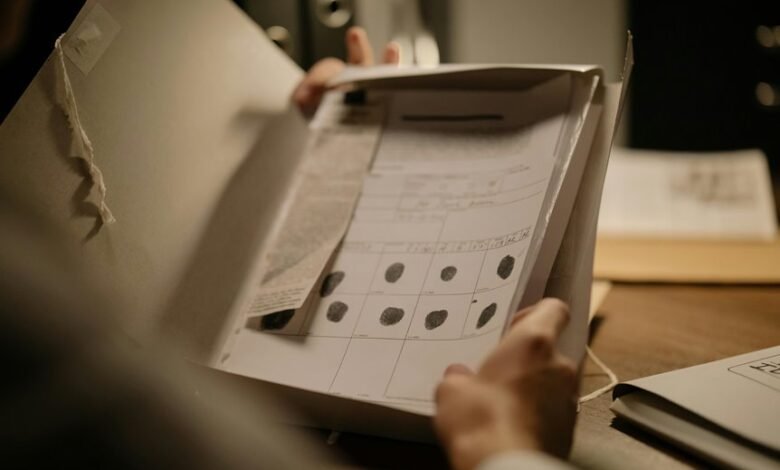
While the concept of hidden identity tracing may seem straightforward, its implications are complex and multifaceted. This process relies on identity verification methods that scrutinize digital footprints left by users.
These footprints can reveal patterns of behavior, location data, and personal information, raising significant concerns about privacy. Understanding these dynamics is essential for individuals seeking autonomy in an increasingly surveilled digital landscape.
The Role of Advanced Technologies in Anonymity
Advanced technologies play a pivotal role in enhancing anonymity within the digital sphere. Innovations such as encryption, virtual private networks, and decentralized networks facilitate anonymity preservation by obscuring users’ digital footprints.
These tools empower individuals to navigate the online realm with greater freedom, reducing the likelihood of surveillance and data tracking. As technology evolves, the potential for enhanced privacy continues to expand, supporting a more anonymous digital existence.
Potential Risks and Vulnerabilities
Although anonymity technologies provide significant benefits, they also introduce potential risks and vulnerabilities that can be exploited by malicious actors.
Data breaches may occur, leading to identity theft, while phishing scams can deceive users into revealing sensitive information.
Furthermore, cyber surveillance techniques can undermine the very purpose of anonymity, exposing individuals to unwanted scrutiny and compromising their freedom and privacy online.
Best Practices for Maintaining Online Privacy
Given the potential risks associated with anonymity technologies, individuals must adopt best practices to safeguard their online privacy.
Implementing data encryption ensures that personal information remains secure against unauthorized access.
Utilizing private browsing modes can minimize tracking by limiting data stored in cookies and browser histories.
Furthermore, regularly updating security settings and being cautious with sharing personal data significantly enhance one’s online privacy posture.
Conclusion
In the ever-evolving landscape of digital interactions, safeguarding personal information is akin to navigating a minefield, where one misstep can lead to catastrophic breaches. The Hidden Identity Tracing Security Report highlights the urgent need for individuals and organizations to adopt advanced technologies and best practices to fortify their online privacy. By remaining vigilant and proactive, they can shield themselves from the shadowy figures of cyber threats, ensuring their identities remain well-guarded in the digital realm.



